The Truvincio Solution is the Right Choice for Small & Medium-Sized Businesses
WHAT TRUVINCIO DOES FOR YOUR BUSINESS
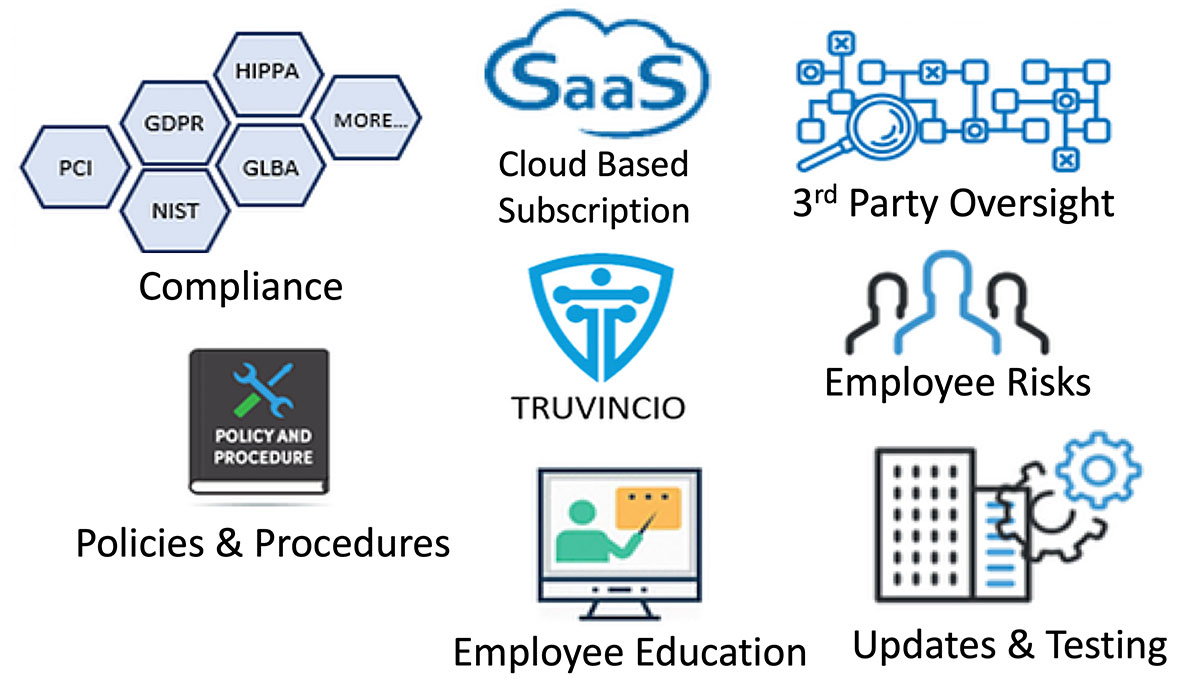
WHAT WE PROVIDE...
- Industry-specific, role-based, online education combined with very effective training methods for every employee.
- Truvincio's policies & procedures align with the requirements of every major security & privacy compliance regimes, including, but not limited to HIPAA, GLBA, PCI, GDPR, ISO 27000, NIST, etc
- Customizable out of the box suite of policies & procedures specifically designed for even the smallest business to empower even the smallest business to achieve a customized program.
- Online audit trail and audit preparation
OUR PROGRAMS ARE...
- Cloud based
- Industry Specific
- Technology agnostic
- Easy to implement and follow - less time away from other work.
- Turnkey - covers the spectrum of requirements.
- Regularly updated to comply with laws and best practices - we take care of it so you don't have to.
- Appropriate to the size of your business and your industry!
CREATE THE RIGHT BEHAVIOR
- The TRUVINCIO online program makes security real and personal to employees. They will make better choices— dramatically reducing the risk of error.
- We help you understand which employee and corporate habits to change and how to make small changes yielding big returns.
- Our online education and training creates good security habits that lead to long- term results.
- We help make your IT efforts more effective. We close the gap between your technology solutions and your employee's mindset that leaves you at risk.
STAND UP TO SCRUTINY
- We provide programs to address every area. One action may cover multiple requirements—simple combinations can avoid the need for multiple programs.
- We give you a simple suite of customizable policies that you and your employees can follow. To be compliant your actions must match your policies.
- Our program is defensible, auditable, and trackable and provides an verification mechanism to demonstrate your good practices to auditors.
- Adds NEW requirements such as those of the SEC and NAIC (National Association of Insurance Commissioners) helping brokers and agents actually work to address their risks.
MAXIMIZE YOUR BUDGET
- Our program will tie together all of your current activities and fill in gaps, improving overall security and improved company efficiency.
- We provide guidance on how to implement your program which gets the results of consulting, without the high costs.
- Our solution covers multiple compliance requirements (PCI, HIPAA, GLB, etc.)—which means less work—less cost.
- Insurance agents can earn 4-7 CE hours annually, in conjunction with implementing our program.
- CE credits for accountants to be introduced in 2019.
Truvincio addresses security & privacy from a very practical side for any SMB. People and Process are the fundamental threats to business which technology can't address no matter the sophistication.
The Truvincio Solution provides the "best value for the dollar" data and privacy security solution in the market! The Truvincio Solution is priced so that even the smallest business can implement the program.

$188,000
average cost of a small business data breach in the US
197 days
time it takes companies to identify a data breach